-
What Is a Cyber Attack?
- Threat Overview: Cyber Attacks
- Cyber Attack Types at a Glance
- Global Cyber Attack Trends
- Cyber Attack Taxonomy
- Threat-Actor Landscape
- Attack Lifecycle and Methodologies
- Technical Deep Dives
- Cyber Attack Case Studies
- Tools, Platforms, and Infrastructure
- The Effect of Cyber Attacks
- Detection, Response, and Intelligence
- Emerging Cyber Attack Trends
- Testing and Validation
- Metrics and Continuous Improvement
- Cyber Attack FAQs
- What Are SMB Null Sessions? Risks, Detection & Prevention
- What Is a DDoS Attack?
- Process Injection Explained: Techniques, Evasion, and Defense
-
What Is a Zero-Day Attack? Risks, Examples, and Prevention
- Zero-Day Attacks Explained
- Zero-Day Vulnerability vs. Zero-Day Attack vs. CVE
- How Zero-Day Exploits Work
- Common Zero-Day Attack Vectors
- Why Zero-Day Attacks Are So Effective and Their Consequences
- How to Prevent and Mitigate Zero-Day Attacks
- The Role of AI in Zero-Day Defense
- Real-World Examples of Zero-Day Attacks
- Zero-Day Attacks FAQs
-
What Is Lateral Movement?
- Why Attackers Use Lateral Movement
- How Do Lateral Movement Attacks Work?
- Stages of a Lateral Movement Attack
- Techniques Used in Lateral Movement
- Detection Strategies for Lateral Movement
- Tools to Prevent Lateral Movement
- Best Practices for Defense
- Recent Trends in Lateral Movement Attacks
- Industry-Specific Challenges
- Compliance and Regulatory Requirements
- Financial Impact and ROI Considerations
- Common Mistakes to Avoid
- Lateral Movement FAQs
- What is a Payload-Based Signature?
-
What is Spyware?
- Cybercrime: The Underground Economy
-
What Is Cross-Site Scripting (XSS)?
- XSS Explained
- Evolution in Attack Complexity
- Anatomy of a Cross-Site Scripting Attack
- Integration in the Attack Lifecycle
- Widespread Exposure in the Wild
- Cross-Site Scripting Detection and Indicators
- Prevention and Mitigation
- Response and Recovery Post XSS Attack
- Strategic Cross-Site Scripting Risk Perspective
- Cross-Site Scripting FAQs
- What Is a Dictionary Attack?
- What Is a Credential-Based Attack?
-
What Is a Denial of Service (DoS) Attack?
- How Denial-of-Service Attacks Work
- Denial-of-Service in Adversary Campaigns
- Real-World Denial-of-Service Attacks
- Detection and Indicators of Denial-of-Service Attacks
- Prevention and Mitigation of Denial-of-Service Attacks
- Response and Recovery from Denial-of-Service Attacks
- Operationalizing Denial-of-Service Defense
- DoS Attack FAQs
- What Is Hacktivism?
-
What Is CSRF (Cross-Site Request Forgery)?
- CSRF Explained
- How Cross-Site Request Forgery Works
- Where CSRF Fits in the Broader Attack Lifecycle
- CSRF in Real-World Exploits
- Detecting CSRF Through Behavioral and Telemetry Signals
- Defending Against Cross-Site Request Forgery
- Responding to a CSRF Incident
- CSRF as a Strategic Business Risk
- Key Priorities for CSRF Defense and Resilience
- Cross-Site Request Forgery FAQs
- What Is Spear Phishing?
-
What Is Brute Force?
- How Brute Force Functions as a Threat
- How Brute Force Works in Practice
- Brute Force in Multistage Attack Campaigns
- Real-World Brute Force Campaigns and Outcomes
- Detection Patterns in Brute Force Attacks
- Practical Defense Against Brute Force Attacks
- Response and Recovery After a Brute Force Incident
- Brute Force Attack FAQs
- What is a Command and Control Attack?
- What Is an Advanced Persistent Threat?
- What is an Exploit Kit?
- What Is Credential Stuffing?
- What Is Smishing?
-
What is Social Engineering?
- The Role of Human Psychology in Social Engineering
- How Has Social Engineering Evolved?
- How Does Social Engineering Work?
- Phishing vs Social Engineering
- What is BEC (Business Email Compromise)?
- Notable Social Engineering Incidents
- Social Engineering Prevention
- Consequences of Social Engineering
- Social Engineering FAQs
-
What Is a Honeypot?
- Threat Overview: Honeypot
- Honeypot Exploitation and Manipulation Techniques
- Positioning Honeypots in the Adversary Kill Chain
- Honeypots in Practice: Breaches, Deception, and Blowback
- Detecting Honeypot Manipulation and Adversary Tactics
- Safeguards Against Honeypot Abuse and Exposure
- Responding to Honeypot Exploitation or Compromise
- Honeypot FAQs
- What Is Password Spraying?
- How to Break the Cyber Attack Lifecycle
-
What Is Phishing?
- Phishing Explained
- The Evolution of Phishing
- The Anatomy of a Phishing Attack
- Why Phishing Is Difficult to Detect
- Types of Phishing
- Phishing Adversaries and Motives
- The Psychology of Exploitation
- Lessons from Phishing Incidents
- Building a Modern Security Stack Against Phishing
- Building Organizational Immunity
- Phishing FAQ
- What Is a Rootkit?
- Browser Cryptocurrency Mining
- What Is Pretexting?
- What Is Cryptojacking?
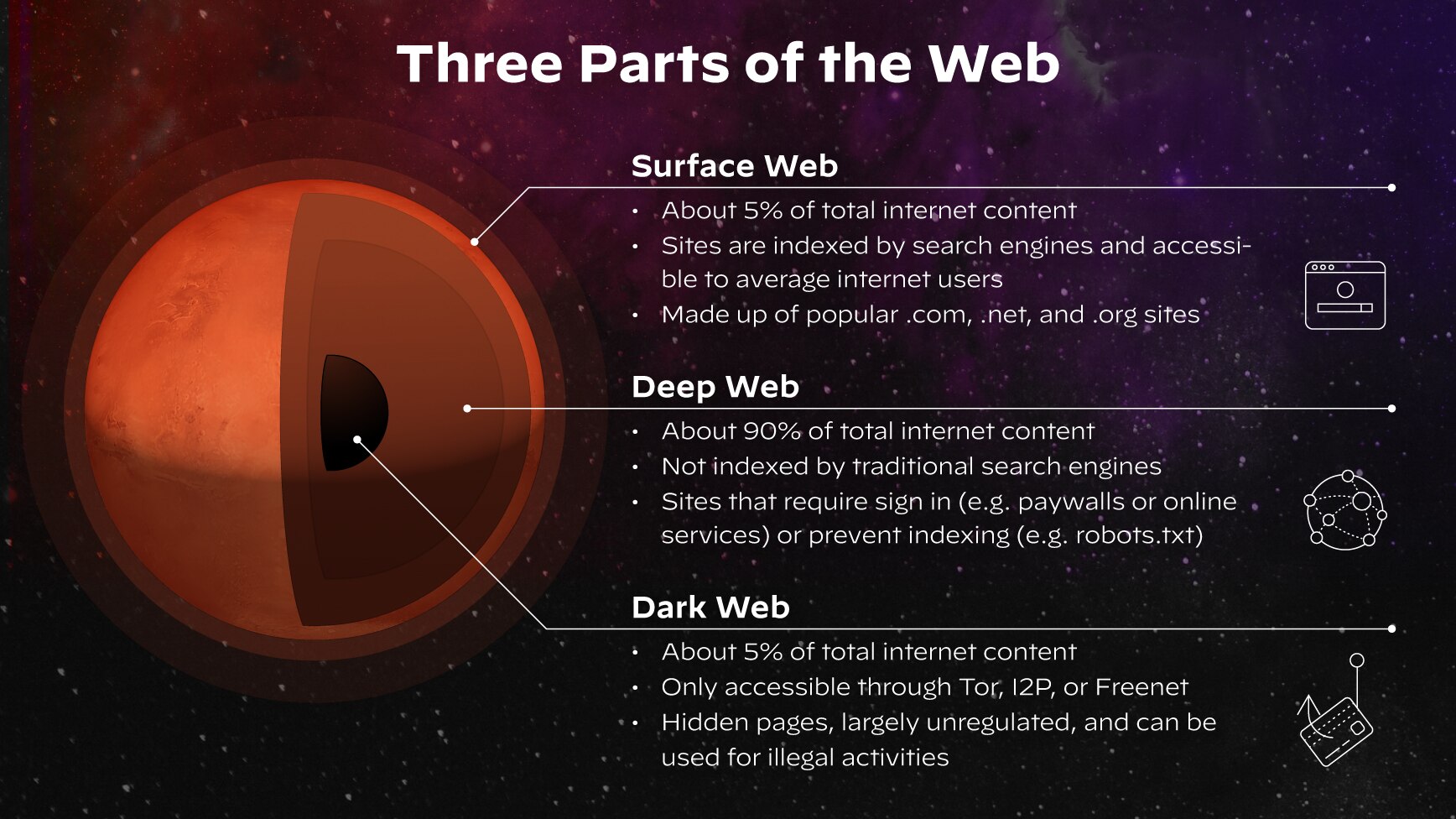
What Is a Dark Web Leak Site?
A dark web leak site (also referred to as the darkweb and darknet) is a hidden website where cybercriminals publish stolen or exfiltrated data — for example, user credentials, databases, proprietary documents, or proofs-of-theft — often to extort victims, sell the information, or show off a breach. These sites commonly include an attacker-controlled contact (a PGP key or chat link), proof samples, and, sometimes, searchable indexes; access is restricted to anonymized networks and often to vetted users or buyers.
Key Points
-
Dark Web Leak Sites: are hidden platforms on networks like Tor used primarily by criminals for extortion, publishing stolen data. -
Double Extortion: involves stealing data first, then encrypting systems, and threatening public disclosure of the leak on the leak site if the ransom is unpaid. -
Top Targets: The Manufacturing sector is the most frequently targeted industry, and the United States is the most impacted country. -
Significant Consequences: Data leaks lead to severe financial losses, regulatory fines (e.g., GDPR), loss of Intellectual Property, and personal risks for employees. -
Best Defense: a proactive strategy is vital, including continuous dark web monitoring and the enforcement of strong security measures such as Multi-Factor Authentication (MFA) and the Principle of Least Privilege (PoLP).
Dark Web Leak Sites Explained
A dark web leak site is a specialized platform built to operate outside the reach of traditional internet indexing and surveillance. They are typically hosted on the Tor network, requiring users to employ the Tor browser to access their randomized (.onion) domain names. This cloaking mechanism ensures the anonymity of both the threat actor hosting the site and the users accessing the stolen data.
The primary evolution of these sites is their purpose: to monetize data through extortion, rather than simply selling it on an underground marketplace. When ransomware groups fail to secure payment for the decryption key, they use the site as a public shaming wall.
Threat actors list the victim organization's name, disclose a partial sample of exfiltrated data, and often set a public countdown timer before releasing the whole cache. This calculated use of reputational damage is a highly effective pressure tactic designed to coerce legal teams and C-suite executives into swift payment.
Evolving Extortion Tactics
Modern threat actors are becoming more aggressive and sophisticated in their extortion methods, moving beyond simple encryption and data leaks. Unit 42 has observed threat actors making unsubstantiated claims of data leakage using old or fake data to pressure victims into paying a ransom.
Attackers are also targeting an expanding array of systems, including critical servers, cloud environments, and hypervisors like ESXi. They have begun using specialized tools, commonly known as “EDR killers,” to disable endpoint security sensors. This tactic enables attackers to rapidly deploy their payloads and execute encryption before an organization can effectively detect and respond to the intrusion.
Ransomware Leak Site Trends
Unit 42 observations from the first quarter of 2025 indicate that threat actors are continually refining their extortion tactics to enhance success rates. The data collected from dark web leak sites shows ransomware remains a significant, adaptive threat targeting high-value victims.
Most Active Ransomware Leak Sites (2025)

Figure 2: RansomHub is the most prolific ransomware group in public reports on leak sites.
Key Observations
According to Unit 42’s 2025 Ransomware Extortion Trends report, RansomHub was the top ransomware group from January to March 2025, marking a rise in the number of aggressive new groups. Ransomware activity increased overall from January to February, mirroring trends from the previous year.
Reported Compromises by Industry

Figure 3: Leak site posts January through March 2025 by industry
Manufacturing remains the most targeted sector due to its reliance on software and low tolerance for downtime. The United States remains the most heavily impacted country.
The Role of Leak Sites in Ransomware Double Extortion
Leak sites did not exist before threat actors began exfiltrating data before encryption; they are an evolution of ransomware, designed to neutralize a company’s backup strategy. By using a dark web leak site, cybercriminals weaponize brand reputation and regulatory compliance against the victim organization.
The Double Extortion Attack Chain
The double extortion method formalizes the use of the leak site into a precise, devastating sequence. This process fundamentally changes the risk calculation for the victim, transforming a technical incident into a public relations crisis. It necessitates a coordinated response across security, legal, and executive teams.
- Initial Access and Exfiltration: The threat actor breaches the network, moves laterally, and copies large volumes of sensitive files to a remote location. This initial data theft is the critical first step that provides the leverage needed for the double extortion.
- Encryption and Ransom Demand: The attacker deploys ransomware to lock critical systems, then delivers a ransom note demanding payment for the decryption key. The note also threatens to publish the already-stolen data.
- Public Shaming and Leak Site Publication: If the victim refuses to pay the ransom, the threat actor publishes a portion of the stolen data on the leak site as proof of compromise. They often include a public countdown timer before releasing the full cache, dramatically increasing the stakes.
Critical Risks Exposed by Data Leak Sites
The appearance of an organization’s data on a leak site is not merely a security breach; it is a full-scale crisis that introduces severe, cascading consequences. These sites turn internal data into a public weapon, profoundly impacting a company’s stability and the safety of its executives. CISOs and risk officers must understand these complex downstream effects.
Financial and Regulatory Fallout
Exposure often triggers an immediate, measurable financial loss that far exceeds any ransom demand. The data leak forces a company to contend with regulatory bodies and public scrutiny simultaneously.
- Compliance Penalties: Violations of regulations such as GDPR, HIPAA, or CCPA result in substantial, non-negotiable fines based on the scope of the leaked personally identifiable information (PII) or sensitive data. Regulators prioritize enforcement when data is carelessly exposed on a public-facing dark web platform.
- Litigation and Recovery Costs: Organizations face costly customer lawsuits, stock price volatility, and substantial expenses for digital forensics, system remediation, and identity protection services. Financial recovery can take years, even after systems are restored.
Corporate Espionage and Competitive Loss
Leak sites transform passive data theft into active competitive sabotage. Stolen corporate secrets are often quickly acquired by rival companies or state-sponsored groups.
- Intellectual Property Exposure: Leaked data often includes proprietary source code, future product roadmaps, or trade secrets that competitors or nation-state actors can instantly exploit. The loss of IP can permanently erode a company's market advantage.
- Strategic Manipulation: Attackers may sell sensitive documents detailing mergers and acquisitions (M&A), client contracts, or internal financial audits to adversarial parties. This provides competitors with actionable insights for competitive bidding or market manipulation.
Executive and Employee Safety Concerns
The risk extends beyond the corporate balance sheet to personal safety and the compromise of identity. Leaked data is frequently used for highly personalized and devastating follow-up attacks.
- Targeted Social Engineering: Compromised C-suite or high-level employee credentials are used to launch spear-phishing and business email compromise (BEC) attacks against partners and clients. These attacks are highly successful because they leverage legitimate, authentic, internal information.
- Doxxing and Extortion: Personal details, including home addresses, travel itineraries, and family contacts, are frequently exposed. This leads to real-world threats, harassment, and intense personal pressure for extortion payments against key personnel.
Anatomy of a Dark Web Leak Site
Understanding the fundamental structure of these hidden platforms is essential for security analysts performing threat hunting and intelligence gathering. Leak sites are specifically designed to facilitate high-volume, anonymous transactions involving compromised digital assets. They are generally organized for maximum searchability by victim name, industry, and data type.
What Data is Most Frequently Leaked?
The inventory of a typical dark web leak site is comprehensive, reflecting the most valuable and sensitive information an organization holds. Threat actors prioritize data that maximizes the victim's perceived risk, thereby increasing the likelihood of a ransom payment.
- Credentials and Access: Stolen account logins, privileged access tokens, and remote desktop protocol (RDP) credentials used for initial access brokerage. These provide low-cost entry points for future attacks.
- Personally Identifiable Information: Large customer or employee datasets, including social security numbers, birth dates, financial account numbers, and medical records. This data carries the highest risk of compliance penalties.
- Proprietary Documents: Internal emails, legal documents subject to attorney-client privilege, source code repositories, and financial projections. Exposure of this data can be strategically devastating to a company's long-term health.
How Threat Actors Maintain Anonymity
Threat actors use a layered approach to ensure their identities, locations, and transactions remain untraceable by law enforcement and intelligence agencies. This reliance on obfuscation is what makes these sites so resilient.
- Tor Network Utilization: The .onion domain structure provides encryption and anonymity by routing traffic through multiple volunteer-run relays globally. This distributed architecture makes tracing the physical location of servers virtually impossible.
- Cryptocurrency Transactions: All monetary exchange for data or ransom is conducted using privacy-focused cryptocurrencies like Monero or Zcash, or laundered via Bitcoin mixers. This ensures transactional records are detached from real-world identities.
Proactive Defense: How Organizations Can Mitigate Dark Web Leaks
An effective defense shifts the focus from post-incident cleanup to preemptive disruption, ensuring that organizational data never reaches the public stage of a dark web leak site. Practitioners must integrate threat intelligence into their defensive controls for real-time risk reduction.
Implementing a Dark Web Monitoring Strategy
Proactive monitoring provides crucial early warning, enabling organizations to take action before a public disclosure. Near-real-time data is essential for effective incident response.
- Continuous Asset Monitoring: Automated tools must constantly scan dark web forums, marketplaces, and leak sites for corporate email addresses, domain names, IP addresses, and brand mentions. This search should specifically target newly listed victims and posted data samples.
- Intelligence Integration: Raw threat intelligence from monitoring should be fed directly into security operation centers (SOCs) to pre-emptively invalidate exposed credentials and block known malicious IP addresses. This closes the back door before an actor can re-enter.
Strengthening Core Security Hygiene
Basic security controls remain the most potent defense against the initial compromise that leads to data exfiltration. Preventing initial access eliminates the possibility of a leak.
- Multifactor Authentication (MFA): Enforce MFA across all high-value accounts, especially for executive access, to neutralize the risk of leaked passwords. Even if credentials appear on a dark web leak site, MFA prevents access.
- Principle of Least Privilege (PoLP): Restrict employee access to only the data absolutely necessary for their job function to limit the scope of exfiltration during a breach. This reduces the amount of valuable data an attacker can steal.
- Microsegmentation: Implement microsegmentation within the network to severely limit a threat actor’s ability to move laterally and exfiltrate large volumes of data. Attackers must work harder to traverse highly segmented environments.
Comprehensive Incident Response Planning
Even with comprehensive defenses, a structured response plan is necessary to manage the crisis when a leak occurs. Legal and communications preparedness is as important as technical remediation.
- Pre-Drafted Communications: Establish internal and external communication plans, including legal and public relations strategies, to deploy immediately upon discovering a mention of a data leak site. Timely and transparent communication is critical for reputation management.
- Containment Procedures: Clearly define and rehearse the technical steps required to contain the data exfiltration pathway and revoke the threat actor's access. The response team must isolate compromised systems rapidly to prevent further data loss.