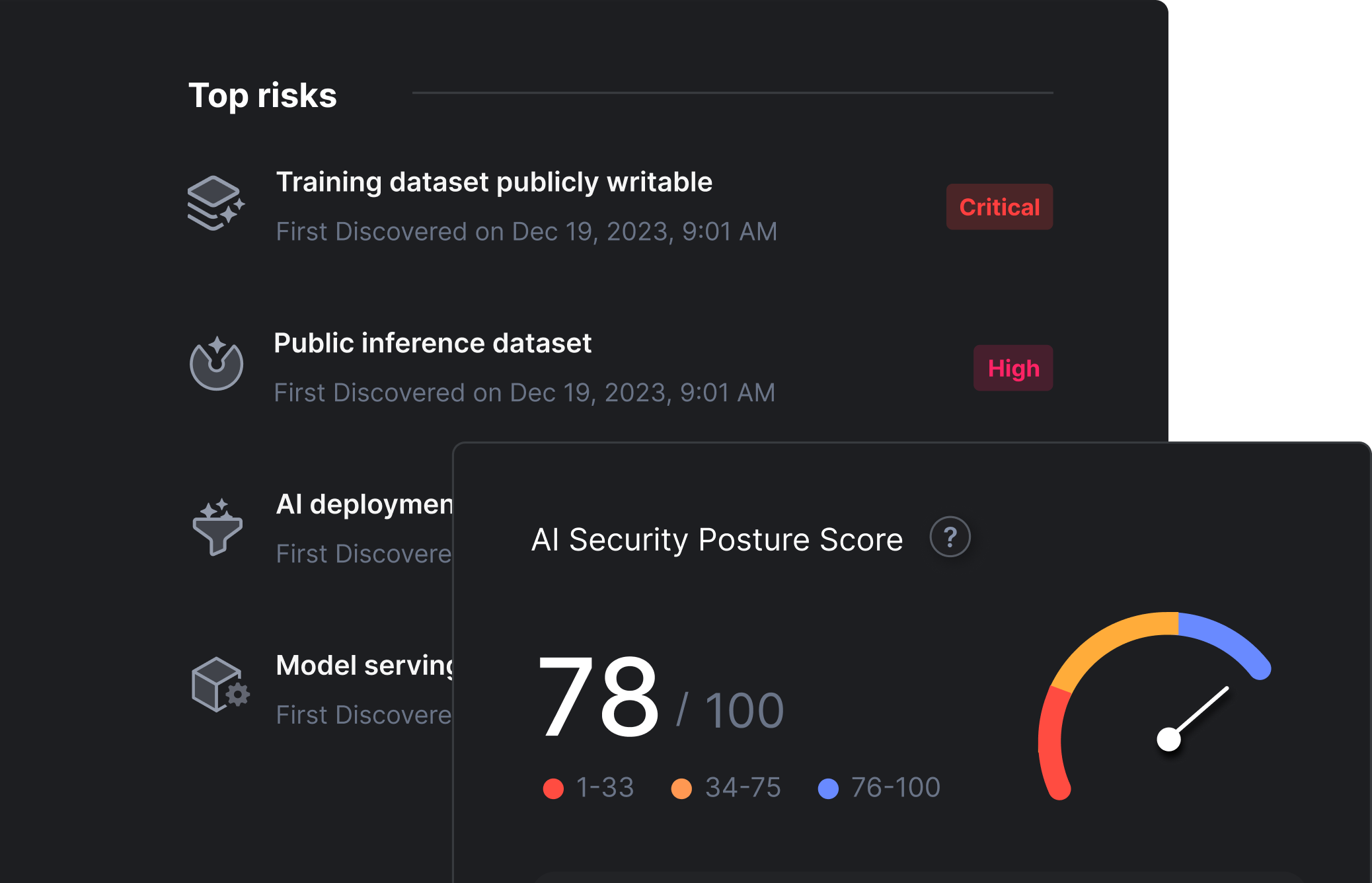
New AI attack vectors
Implementing new pipelines and infrastructure together with lack of unified visibility make organizations susceptible to new attacks.
New AI attack vectors
Implementing new pipelines and infrastructure together with lack of unified visibility make organizations susceptible to new attacks.
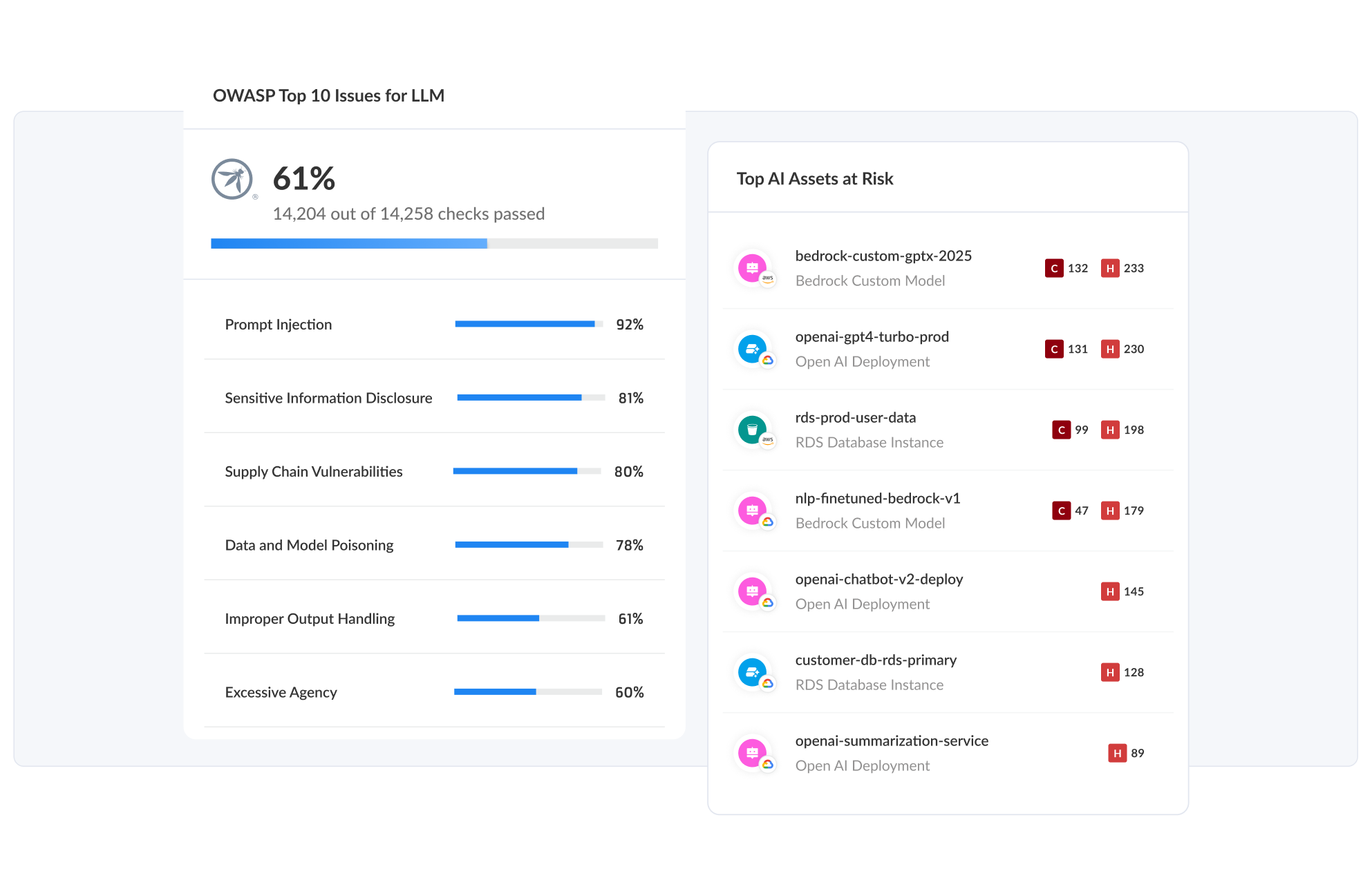
Dealing with model sprawl issues
Lack of AI inventory can lead to shadow AI models, compliance violations and data exfiltration through AI-powered applications.
Governance is lacking
New AI-focused legislation mandates strict controls around AI usage and customer data that is fed into AI powered applications.
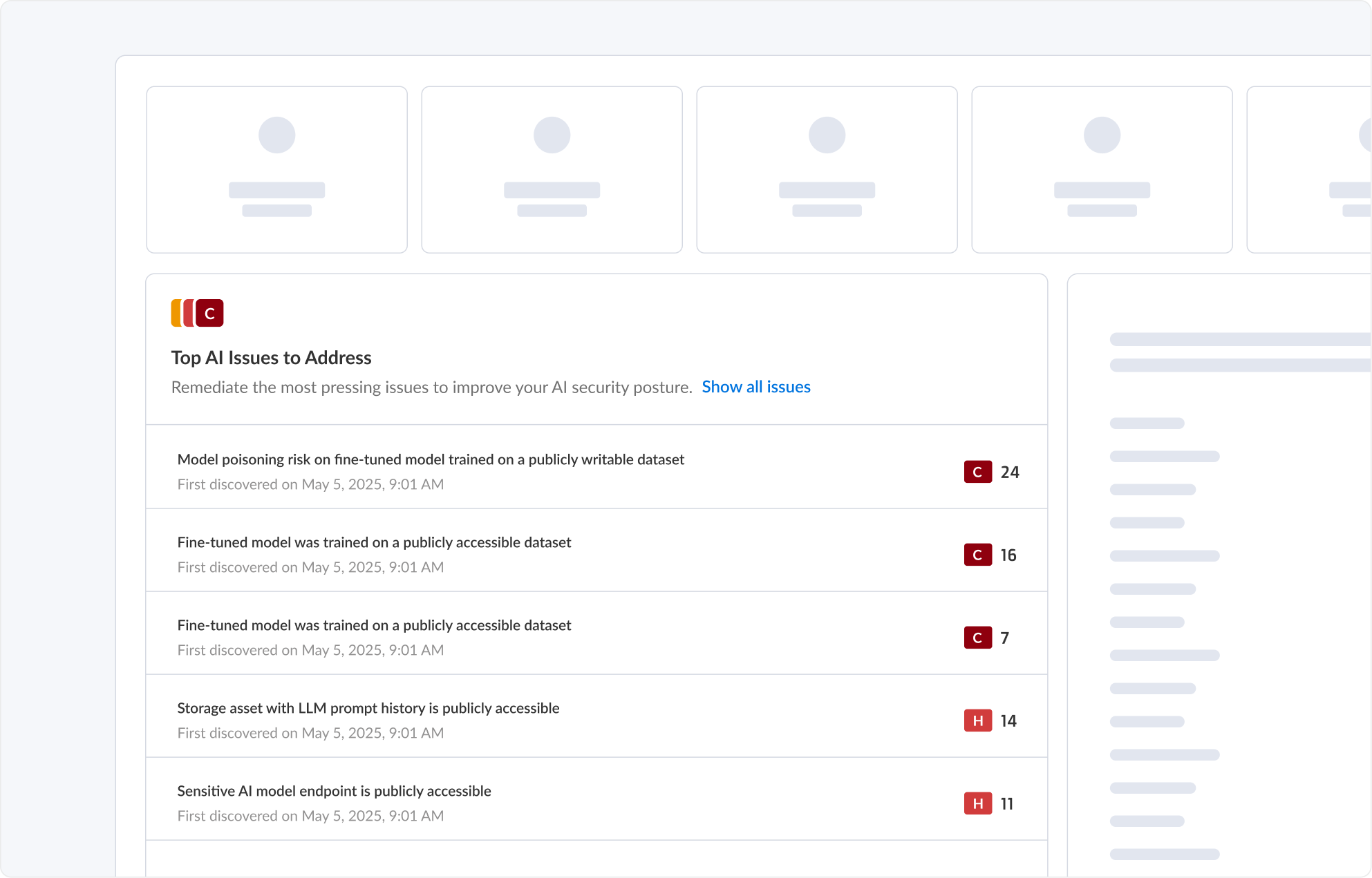
Maximize the transformative benefits of AI and large language models (LLMs) without putting your organization at risk. Prisma® Cloud AI Security Posture Management (AI-SPM) gives you visibility and control over the three critical components of your AI security — the data you use for training or inference, the integrity of your AI models and access to your deployed models.
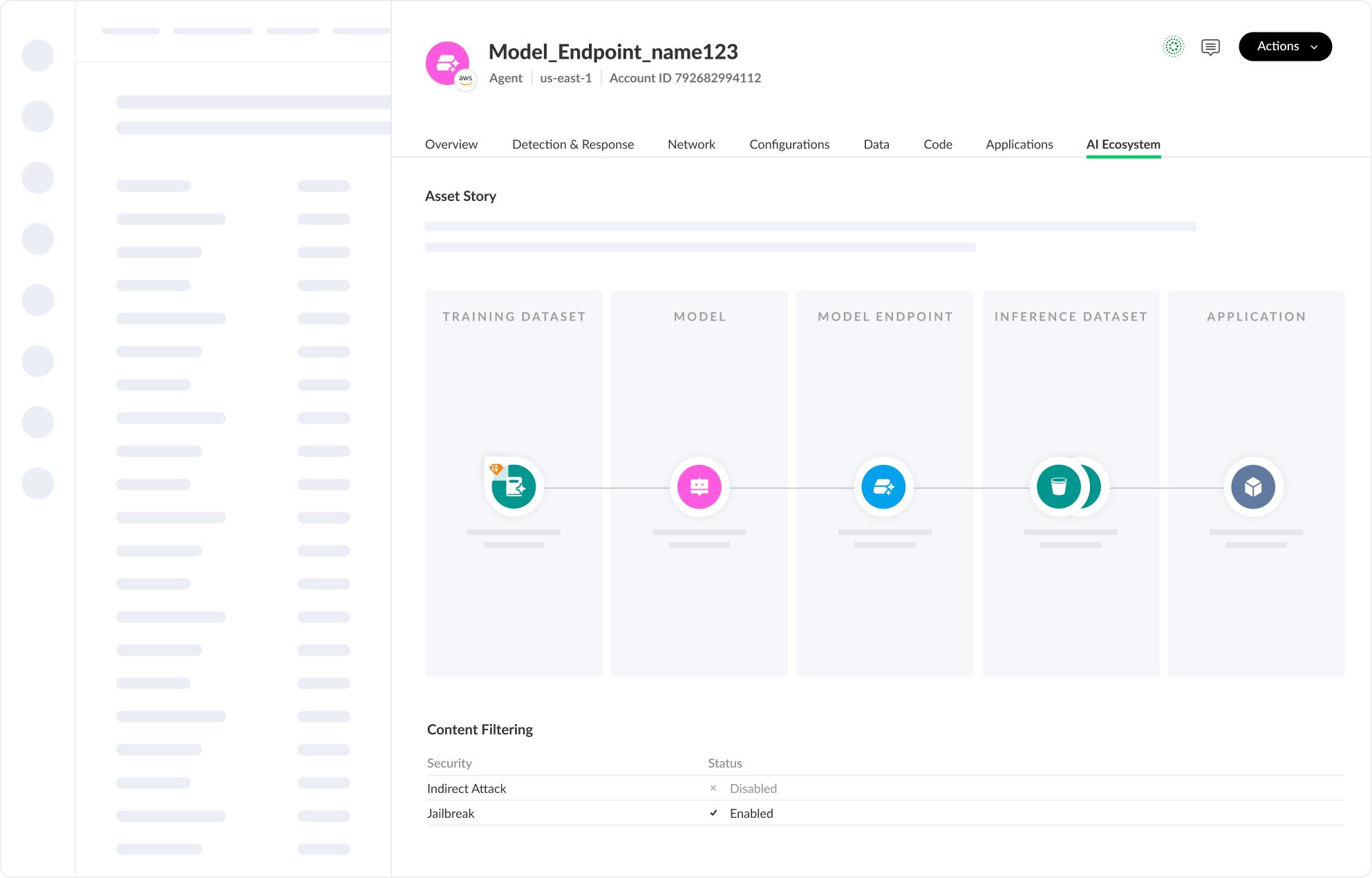
Discover all AI applications, models and associated resources. Identify and trace lineage of AI components used in applications.
AI App stack discovery
Discover all AI applications, models and associated resources.
AI lineage
Identify and trace lineage of AI components and data sources used in applications.
Model inventory
Catalog AI models deployed and identify updates.
Identify vulnerabilities in the AI supply chain, and find misconfigured models and related cloud resources that can lead to manipulation, misuse and theft.
Prevent model compromise and theft
By identifying risks of adversaries to create a functional equivalent.
Find misconfigurations
By reducing overprivileged compute instances and models.
Avoid insecure plug-in design
By identifying overprivileged and vulnerable agents/workloads.
Manipulating model data can introduce vulnerabilities and biases, expose data, and lead to data privacy violations, compliance and security risks.
Classify the AI stack
Identify where sensitive data exists in training and reference data, libraries, APIs, and data pipelines that power AI models.
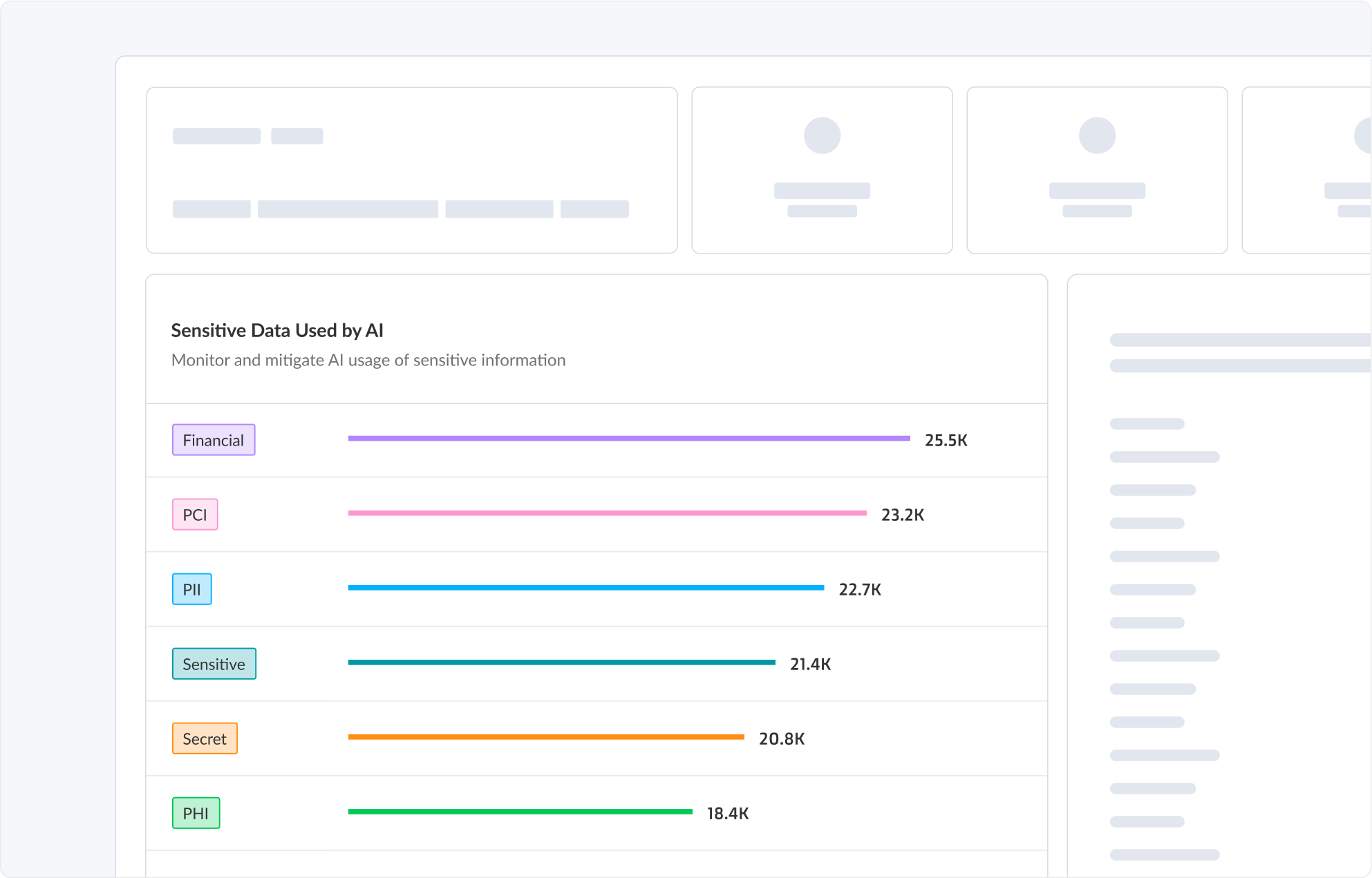
Monitor sensitive data
Monitor and govern data exposure, poisoning risk, privacy violations and security breaches.
Prioritize vulnerabilities
In infrastructure that host AI that is accessing sensitive data.