- Best Splunk Competitors & Alternatives for 2026
- What is Security Analytics?
- Best Exabeam Alternatives: Top Competitors in 2026
- Best Datadog Alternatives & Competitors for 2026
- Best SIEM Tools for 2026: Compare 10 Leading Platforms
- What are SIEM Use Cases?
- What is Security Information and Event Management (SIEM) Integration?
- What is SIEM Logging?
- What Is Security Event Management (SEM)?
- What is a SIEM Solution in a SOC?
- How Do SIEM Tools Benefit SOC Teams?
-
What Is the Role of AI and ML in Modern SIEM Solutions?
- The Evolution of SIEM Systems
- Benefits of Leveraging AI and ML in SIEM Systems
- SIEM Features and Functionality that Leverage AI and ML
- AI Techniques and ML Algorithms that Support Next-Gen SIEM Solutions
- Predictions for Future Uses of AI and ML in SIEM Solutions
- Role of AI and Machine Learning in SIEM FAQs
-
What is Cloud SIEM?
- Why Use a Cloud SIEM?
- How SIEM Interacts with Cloud Environments and SaaS Applications
- Core Cloud SIEM Features and Capabilities
- Cloud SIEM Deployment Models
- On-Premise vs. Cloud SIEM Deployment
- Key Steps for Implementing Cloud SIEM
- Cloud SIEM Challenges
- Considerations of a Cloud Native SIEM Solution
- Cloud SIEM FAQs
- What Is Security Information Event Management (SIEM) Software?
- What Are Security Information and Event Management (SIEM) Tools?
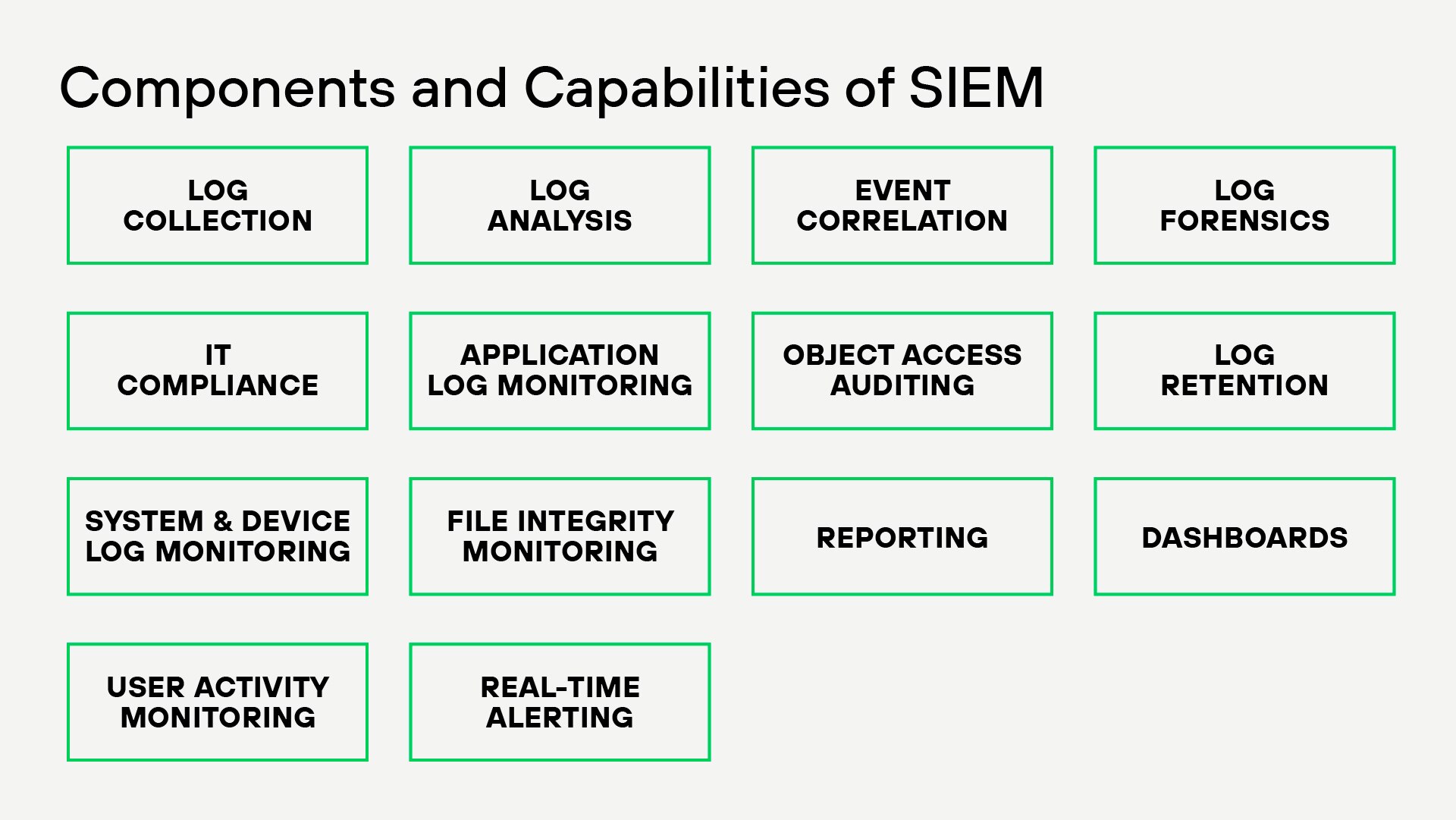
What Is Security Information and Event Management (SIEM)?
SIEM, which stands for Security Information and Event Management, is a cybersecurity solution that correlates log and event data from systems across an IT environment. SIEMs combine two critical functions, Security Information Management (SIM) and Security Event Management (SEM), providing organizations with the following advantages:
- Enhanced threat detection and response
- Improved incident investigation with detailed log data
- Simplified regulatory compliance
- Centralized visibility into network security
Implemented as software, hardware, or managed services, SIEM systems are central to security operations centers (SOCs), which detect, investigate, and respond to security incidents.
SIEM: The Foundation for XSIAM
XSIAM (Extended Security Intelligence and Automation Management) represents the evolution of SIEM, which was built to overcome the limitations of traditional SIEM systems.
SIEM is foundational, focusing on collecting and correlating logs and event data to detect threats. Still, it often requires extensive manual work, rules tuning, and separate tools for investigation and response.
XSIAM builds on and advances SIEM, serving as its modern alternative. It is a next-gen security operations platform that ingests and analyzes data like a SIEM, but it goes further by:
- Integrating data ingestion, analytics, automation, and response in a single platform.
- Using machine learning and behavioral analytics to reduce noise and prioritize real threats.
- Delivering autonomous SOC capabilities, reducing reliance on human effort for repetitive tasks.
XSIAM automates, accelerates, and unifies the entire security operations lifecycle for better speed, accuracy, and scale.
How SIEM Works
SIEM collects and analyzes security data from various sources such as firewalls, servers, cloud platforms, network devices, and third-party tools. It aggregates this information into a centralized platform to identify patterns and unusual activities in real time.
Collected data is then standardized into a common format, making it easier to analyze. It applies predefined rules and algorithms to identify patterns and relationships across data points, such as linking failed login attempts to suspicious IP activity.
SIEM continuously monitors data streams for anomalies, suspicious behaviors, or known indicators of compromise (IoCs). Advanced SIEMs use machine learning to detect unusual patterns, such as abnormal user activity or network traffic spikes. When potential threats are identified, SIEM generates alerts based on severity and urgency.
SIEM assigns a risk score to each event based on predefined rules, machine learning insights, and threat intelligence. This helps SOC teams focus on high-priority threats and reduce false positives.
Many SIEM platforms integrate with SOAR tools to enable automated actions like quarantining compromised devices, blocking malicious IP addresses, and sending alerts to stakeholders.
Historical logs and incident data are stored, allowing security teams to trace the source of attacks, analyze the timeline and scope of an incident, and identify root causes and vulnerabilities.
Reports are generated to meet regulatory compliance requirements (e.g., GDPR, HIPAA, PCI DSS). This provides insights into security performance, helping organizations improve their overall posture.
Key Functions and Benefits of SIEM
SIEM is used by Security Operations Center (SOC) teams, IT administrators, and Managed Security Service Providers (MSSPs) to maintain comprehensive, resilient security solutions in organizations of all sizes.
Data Aggregation and Normalization
SIEM gathers data from various sources and converts it into a unified format, providing a comprehensive view of an organization's security environment. This normalization standardizes logs and data sets, enhancing pattern recognition and anomaly detection for security threats. By consolidating data, SIEM improves monitoring accuracy, ensures critical alerts are not missed, and supports compliance reporting with audit-ready datasets.
Real-Time Monitoring
Regularly monitoring network traffic and user behavior helps organizations quickly identify unusual activities that may signal an attack or unauthorized access. This approach allows security teams to respond swiftly and prevent data breaches.
Continuous monitoring also detects subtle or complex attacks that might evade traditional methods. Advanced analytics and machine learning enhance detection, identify new threats, and predict future vulnerabilities. This process protects sensitive data and supports compliance by maintaining a clear record of security events and responses.
Threat Detection
SIEM tools help organizations analyze security logs to spot signs of cyberattacks, insider threats, or rule violations. They review large amounts of security data to detect unusual activities that may indicate a breach, focusing on small issues like changes in user behavior.
These systems use threat intelligence feeds to compare known attack patterns with new behaviors. This improves their ability to identify threats and respond quickly, giving security teams real-time alerts and automated responses. SIEM tools help organizations stay prepared against evolving cyber threats by improving detection methods and using up-to-date threat information.
Incident Response
SIEM systems help respond to security threats, either automatically or manually. Key benefits of SIEM for incident response include:
- Faster detection and containment of threats.
- Reduced manual workload through automation.
- Improved accuracy with advanced analytics and fewer false positives.
- Enhanced coordination among SOC teams.
With automated workflows, SIEM handles repetitive tasks like notifying users and containing threats quickly, reducing response times and limiting the spread of attacks. Manual responses let security analysts investigate unique or needful thought incidents, ensuring responses fit each specific threat.
This thorough approach to incident handling is vital for reducing downtime and lessening the effects of security issues on critical operations.
Compliance Reporting
SIEM solutions continuously gather and normalize vast arrays of data, ensuring that information is accurate and readily accessible for compliance audits. Ultimately, the streamlined processes made possible by SIEM solutions enhance compliance and free up valuable resources, allowing security teams to focus on more strategic security tasks.
By automating the reporting process, SIEMs help organizations:
- Simplify adherence to regulatory requirements (e.g., GDPR, HIPAA, PCI DSS) by generating audit-ready reports
- Reduce the significant burden on IT and compliance teams.
- Avoid the potential pitfalls of manual data compilation, which can often lead to errors or omissions.
- Maintain a comprehensive audit trail, crucial for demonstrating compliance and accountability to regulators.
Role of AI and ML in SIEM
Modern SIEM tools use AI and machine learning (ML) to:
- Enhance threat detection
- Reduce false alarms
- Help predict security breaches
- Learn from data over time, improving accuracy and reducing unnecessary alerts
- Enable automated responses to threats without human input, freeing up security experts to focus on more complex issues
- Provide insights into potential vulnerabilities
SIEM Integration
By seamlessly connecting with various security technologies such as firewalls, intrusion detection systems, and vulnerability scanners, SIEM enhances the capability to detect and respond to potential threats with greater precision. This process is achieved by gathering extensive data from multiple sources, which ensures smooth interoperability and provides a cohesive understanding of the threat landscape.
As the integration extends further, SIEM systems often work with security orchestration, automation, and response (SOAR) platforms. This collaboration facilitates the automation of security tasks, ensuring that alerts and potential threats are addressed promptly and adequately.
These advancements streamline operations within security teams and elevate the efficiency and responsiveness of an organization's overall security posture. Integrating SIEM with existing technologies is essential for building a resilient defense mechanism capable of adapting to the dynamic nature of cyber threats.
SIEM Use Cases
SIEM is an invaluable tool, offering numerous SIEM use cases to benefit organizations of all sizes, for organizations of all sizes.
Threat Detection and Response
- Real-Time Threat Monitoring: SIEM systems detect unusual activities such as login anomalies, lateral movement, or brute-force attacks.
- Use Case: Detecting ransomware attacks by monitoring abnormal file encryption activity.
- Benefit: Rapid identification of security breaches and automated responses to mitigate damage.
- Strategy:
- Define use cases and correlation rules based on common attack patterns (e.g., brute force, privilege escalation).
- Integrate threat intelligence feeds to enrich event data.
- Use machine learning to detect anomalies.
Insider Threat Detection
- Behavioral Analytics: SIEM analyzes user behaviors to flag unusual activities, such as accessing sensitive files outside business hours.
- Use Case: Identifying an employee attempting to exfiltrate company data to external drives.
- Benefit: Protection against data breaches caused by malicious or negligent insiders.
- Strategy:
- Implement User and Entity Behavior Analytics (UEBA) for monitoring user activity.
- Set baselines for normal behavior and trigger alerts for deviations.
- Log and analyze privileged account activities.
Advanced Persistent Threat (APT) Detection
- Pattern Recognition: SIEM systems identify multi-stage attacks where hackers establish a foothold and escalate privileges.
- Use Case: Recognizing the subtle signs of an attacker conducting reconnaissance within a network.
- Benefit: Early detection of complex, prolonged attacks.
- Strategy:
- Use multi-layered correlation rules to identify long-term attack sequences.
- Monitor endpoints, emails, and network traffic for subtle intrusion signs.
- Leverage external threat intelligence to identify indicators of compromise (IoCs).
Forensic Investigation
- Log Correlation: SOC teams can trace the source of an incident by analyzing historical logs.
- Use Case: Investigating a breach to determine how attackers gained entry and the scope of the attack.
- Benefit: Better post-incident analysis for improved defenses.
- Strategy:
- Ensure logs are indexed and stored for extended periods (based on regulatory requirements).
- Use advanced search capabilities to trace the origin of incidents.
- Cross-correlate data from multiple sources for root cause analysis.
Endpoint Monitoring and Protection
- Comprehensive Endpoint Logs: SIEM collects data from endpoint detection tools to provide a unified view of device activity.
- Use Case: Detecting malware on an endpoint that communicates with known malicious IPs.
- Benefit: Enhanced endpoint security through centralized monitoring.
- Strategy:
- Combine SIEM with endpoint detection and response (EDR) tools for enhanced visibility.
- Set up alerts for malware, unauthorized access, and suspicious file changes.
Cloud Security Monitoring
- Cloud Integration: Modern SIEMs integrate with cloud platforms like AWS, Azure, and Google Cloud to monitor cloud-native threats.
- Use Case: Identifying misconfigured storage buckets or detecting unusual API calls in cloud environments.
- Benefit: Protects cloud infrastructure from unauthorized access and misconfiguration.
- Strategy:
- Integrate cloud-native SIEM tools with major platforms (e.g., AWS, Azure, GCP).
- Use APIs and connectors to monitor cloud activity in real time.
Detecting Lateral Movement
- Network Traffic Analysis: SIEM tracks traffic patterns to identify attackers moving laterally within a network.
- Use Case: Flagging unauthorized communication between servers that typically do not interact.
- Benefit: Prevents attackers from escalating privileges or accessing critical systems.
- Strategy:
- Monitor east-west traffic within the network for unusual communication patterns.
- Implement network segmentation to limit lateral movement.
- Use decoy techniques like honeypots to identify attackers.
Phishing Detection
- Email Log Analysis: SIEM tools analyze email traffic for indicators of phishing attempts.
- Use Case: Identifying mass phishing emails sent to employees with malicious links.
- Benefit: Reduces the risk of credential theft and malware infections.
- Strategy:
- Monitor email gateways and analyze headers for spoofing or malicious links.
- Cross-check attachments with threat intelligence databases.
Third-Party Risk Monitoring
- Supply Chain Security: SIEM systems monitor access logs from third-party vendors to detect abnormal activities.
- Use Case: Detecting a compromised vendor account accessing sensitive internal systems.
- Benefit: Protects against risks introduced by external partners.
- Strategy:
- Monitor third-party access to critical systems through log correlation.
- Enforce strict access policies and monitor vendor activities in real time.
Distributed Denial of Service (DDoS) Detection
- Traffic Anomalies: SIEM tools monitor unusual spikes in network traffic indicative of DDoS attacks.
- Use Case: Detecting volumetric attacks aimed at overwhelming a web application.
- Benefit: Enables quick mitigation to maintain service availability.
- Strategy:
- Monitor network traffic for volumetric spikes.
- Use rate-limiting and blacklisting features to mitigate attacks.
Security Orchestration and Automation
- SOAR Capabilities: Some SIEM systems integrate Security Orchestration, Automation, and Response (SOAR) to execute automated playbooks.
- Use Case: Automatically quarantining an endpoint upon detecting malware.
- Benefit: Accelerates response time and reduces manual workload.
- Strategy:
- Integrate SOAR platforms with your SIEM to automate common workflows.
- Build playbooks for repetitive tasks like quarantining devices or notifying stakeholders.
How to Choose a SIEM Solution
When choosing a SIEM solution, consider deployment options:
- On-Premises vs. Cloud-Based: Decide between self-hosted SIEM systems or cloud-based solutions depending on your infrastructure needs.
- Managed Security Services (MSSP): MSSPs offer expertise in deploying and managing SIEM systems for organizations with limited resources.
Best Practices for SIEM Implementation
Implementing a SIEM system involves several crucial steps, or best practices, to ensure its effectiveness and alignment with organizational security goals.
- Define Objectives: Start with specific use cases and expand as the organization matures.
- Integrate Data Sources: Ensure that all relevant systems (e.g., firewalls, endpoints, applications) feed into the SIEM.
- Tailor Correlation Rules: Customize rules based on your organization’s unique risks and environment.
- Train SOC Teams: Provide training on interpreting SIEM alerts and using advanced features.
- Review Regularly: Continuously optimize configurations and update correlation rules to adapt to new threats.
SIEM vs Other Security Solutions
The cybersecurity world is filled with many tools, and distinguishing between solutions like SIEM and other security technologies is critical for building an effective defense strategy.
XDR Vs. SIEM
As organizations face increasingly sophisticated cyber threats, understanding the differences between SIEM and XDR is essential to choosing the right approach for threat detection and response.
XDR offers a modern integrated approach to threat detection and response, covering a more comprehensive range of data sources and providing real-time capabilities. SIEM focuses more on log and event management, historical analysis, and compliance reporting.
Organizations should consider their specific security needs and existing infrastructure when choosing between the two. Many organizations use a combination of XDR and SIEM for comprehensive security monitoring and incident response.
SOAR vs SIEM
SOAR and SIEM are vital components of cybersecurity. Although each serves distinct purposes, they do work together.
Ultimately, The differences between SOAR and SIEM relate to threat detection, analysis and response.
SIEM primarily emphasizes data collection, monitoring, and analysis of security logs and data. It generates alerts when potential security issues are detected, whereas SOAR automates responses to these security threats and manages the alerts that arise from them. While some SIEM solutions include basic automation features, certain SOAR platforms provide threat intelligence.
EDR vs SIEM
As organizations strengthen their cybersecurity posture, it’s vital to compare EDR and SIEM, two distinct solutions that serve different purposes in identifying and responding to threats. EDR (Endpoint Detection and Response) monitors servers, workstations, and mobile devices to detect and respond to security incidents, providing detailed endpoint protection. SIEM collects and analyzes security events across the network to assess security posture. Many organizations use EDR and SIEM together.
What is Cloud SIEM?
Cloud SIEM leverages cloud infrastructure to provide scalable, flexible, cost-effective security monitoring and threat detection across an organization's network. It centralizes and analyzes large volumes of security data from various sources in real time, enabling rapid detection and response to threats.
Cloud SIEM solutions offer enhanced scalability, easier deployment, and improved accessibility, making them ideal for modern, distributed, and hybrid IT environments.
The Evolution of SIEM
The evolution of SIEM reflects the cybersecurity landscape's shift from reactive to proactive threat management. Modern SIEM solutions focus on automation, AI-driven insights, and scalability, enabling organizations to address today’s complex and fast-evolving threats effectively.
1990s
As businesses connected to the internet, firewalls alone couldn’t handle growing threats. Security teams needed tools to gather and prioritize alerts across networks, leading to the creation of SIEM by combining log management (SIM) and real-time monitoring (SEM).
Early 2000s
Initial SIEM solutions focused on centralizing alerts and compliance reporting but lacked scalability and relied on manual processes, limiting their effectiveness.
Advancements
Over time, SIEM evolved with real-time monitoring, advanced analytics, and machine learning, enabling faster threat detection and response.
Today
Modern SIEM platforms use AI and integrate with automation tools like SOAR to streamline workflows, making them essential for proactive and efficient security operations.
The Future of SIEM
It's important to understand that changes in technology and new security threats will influence the future of SIEM. As cybersecurity continues to improve, SIEM solutions will adapt to effectively detect, handle, and respond to new threats.
Mitigating today’s threats requires a radically new approach to security operations. The future of SIEM is likely to be shaped by several key trends and advancements in the field of cybersecurity:
- Integration with artificial intelligence and machine learning
- Cloud-native and hybrid deployments
- User and entity behavior analytics (UEBA)
- Threat intelligence integration
- Automation and orchestration
- Enhanced user experience and visualization
- Compliance and privacy management
- Integration with XDR
SIEM FAQs
SIEM tools do not directly prevent cyberattacks; instead, they play a critical role in detecting and responding to security threats in real time. By collating and analyzing data from various network sources, SIEM systems provide valuable insights that help security teams identify unusual patterns and potential breaches before they escalate. This timely detection is essential in minimizing the impact of security incidents and preventing them from causing severe damage to an organization's infrastructure. While traditional SIEM focuses on detection and analysis, modern SIEM solutions integrated with Security Orchestration, Automation and Response (SOAR) capabilities can initiate automated preventive actions, such as:
- Automatically blocking suspicious IP addresses
- Quarantining affected systems
- Disabling compromised user accounts
- Updating firewall rules in real-time
- Triggering additional authentication requirements
Additionally, SIEM's historical analysis capabilities help organizations learn from past incidents and strengthen their preventive measures by:
- Identifying security gaps and vulnerabilities
- Refining security policies
- Improving threat detection rules
- Enabling proactive threat hunting
- Enhancing security awareness training based on actual incident patterns
SIEM offers comprehensive logging and monitoring capabilities, aiding in both immediate response and long-term security posture improvement, ultimately contributing to an organization's overall cyber attack prevention strategy.
