Innovation is only as good as your visibility. As organizations rapidly adopt AI agents to automate workflows and enhance productivity, too often, security teams are forced to fly at machine speed without a flight plan. The nondeterministic nature of AI agents means that agents can interact with organizational systems and data in unpredictable ways, introducing new security risks.
When an AI agent performs a task, it often relies on Model Context Protocol (MCP) servers to act as vital bridges to enterprise data sources and systems. However, MCPs lack consistent authentication and security controls, and they may not even be visible to security teams. Developers can, and do, easily download open-source and other MCP servers from public registries to enable their agents to access data sources. These unprotected MCPs can become prime targets for attackers.
Without visibility and access controls, CISOs and security teams are blind to which target resources (such as databases, cloud environments, SaaS applications) AI agents are actually accessing.
Below, we’ll cover how these expanded capabilities for the Secure AI Agents solution bring these vital bridges out of the shadows, enabling security teams to address the challenge of controlling access to internal and external data by helping to secure MCP servers.
Basic MCP Security Controls Aren’t Enough
While many organizations rely solely on native built-in security configurations for MCP servers. These native controls can discover MCP servers or monitor agent activity, but they may not provide the visibility, identity context or access governance enterprises need. Here’s why:
- Lack of Native Authentication: A vast number of MCP servers in the wild (such as internal developer tools or community prototypes) ship with zero built-in authentication. For example, Bloomberry research found that 38% of MCP servers have no authentication.
- Identity Blind Spots: Even when an MCP server uses native OAuth 2.1, the standard authorization framework that many applications use to grant limited access to data and systems, it may only authenticate the human user’s delegated consent. The AI agent itself remains invisible to identity and access management, or IAM, making it harder for security teams to govern the agent or easily trace actions back to it.
- Long-Lived Tokens: Native OAuth 2.1 setups can leave long-lived access and refresh tokens sitting with the AI agent. If the agent experiences a memory compromise or prompt injection, these standing tokens can be stolen and exploited.
- Fragmented Policies: With native authentication, every MCP server may dictate its own security scopes, token lifetimes and audit logs. If an enterprise uses 10 different MCP servers, security teams are forced to manage 10 completely disjointed policy and compliance surfaces.
Unmanaged MCP servers can also create new paths for risk. They may make agents more vulnerable to prompt injection, where malicious code is injected into prompts to hijack agents. They can also include supply-chain attacks and credential theft, where downloaded MCPs contain malicious code that steals credentials or later introduces risk through “rug-pull” updates. Privilege escalation is another concern, where over-scoped tokens allow attackers to pivot directly into databases and repositories. In more serious cases, unmanaged MCP servers may also create exposure to remote code execution, or RCE, where infiltrated MCP servers become entry points for RCE attacks on local machines or allow compromised agents to extract sensitive data.
Without clear visibility into which AI agent acted on behalf of which user, with which permissions, or against which resource, security teams may find it nearly impossible to safely limit an agent’s access or control the specific tools it executes through MCP servers.
How an Identity-Focused Approach Secures MCP Servers
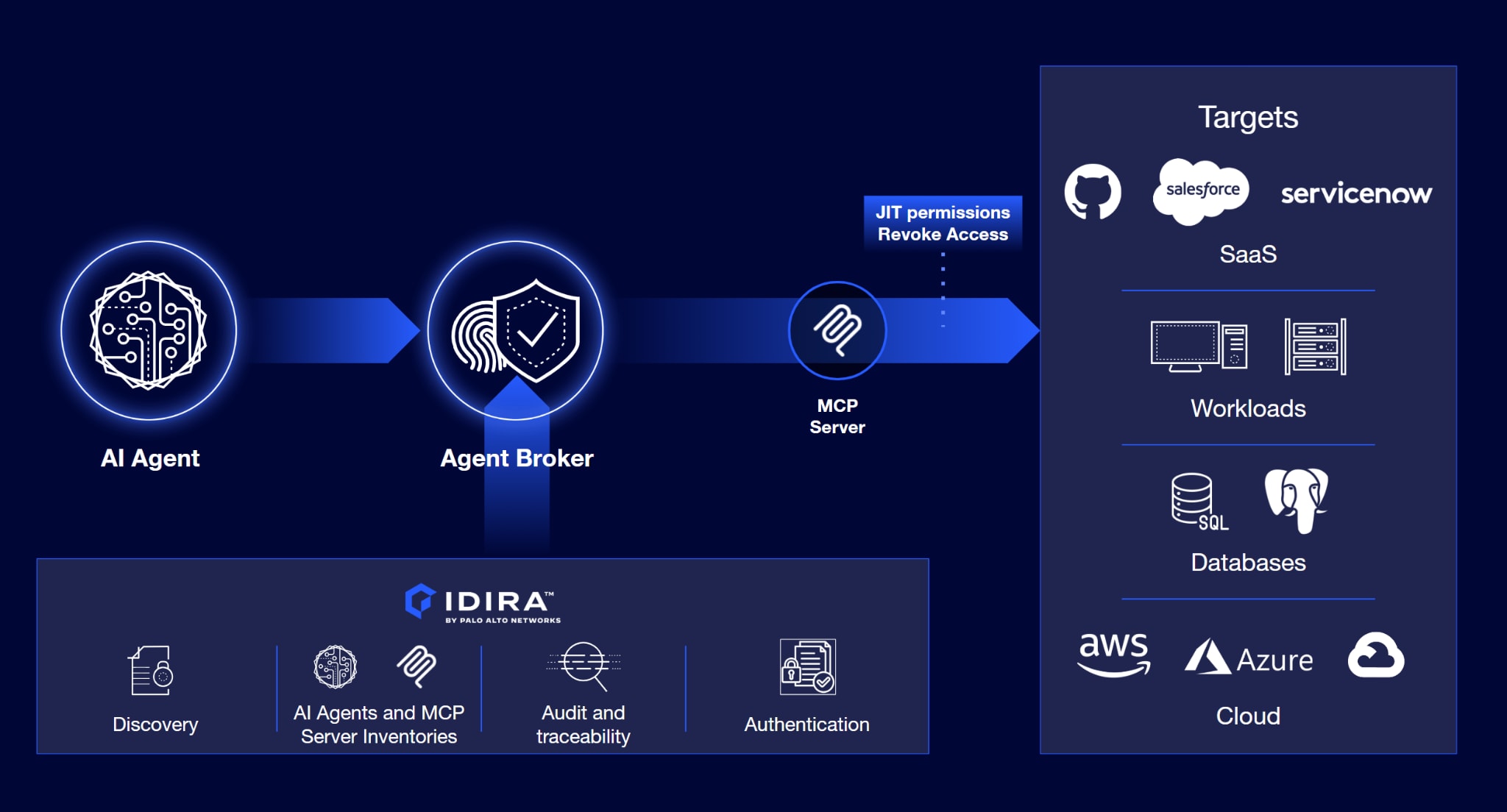
MCP servers act as bridges between AI models and agents to the external data sources and tools that the agents want to access. In these scenarios, the agent identity broker sits between the AI agent and the remote MCP server.
In the Secure AI Agents solution, the agent identity broker can act as the authorization server for the MCP. Instead of allowing the agent to directly hold credentials to access the MCP, the agent’s communications pass through the agent identity broker. The broker can then securely proxy the request to the target MCP server.
This changes the control point. Security teams can move from trying to manage fragmented MCP access on a server-by-server basis to applying centralized identity security controls to agent activity.
For example, when the agent is registered and authenticates to the identity broker that’s working on behalf of a user through OAuth 2.1, Secure AI Agents can help centralize authorization instead of leaving access decisions fragmented across individual MCP servers.
New, Expanded Capabilities Strengthen MCP Security
Secure AI Agents helps security teams bring order to agentic AI by discovering agents, governing MCP access, monitoring activity and enforcing identity security controls from one solution. Here’s how it provides the guardrails that teams need to innovate safely:
1. See More with Centralized Inventory and Discovery
Managing AI sprawl starts with knowing what exists. Secure AI Agents offers a unified view of AI agents deployed across an organization, whether they are built on AWS, Azure, Copilot, OpenAI or Claude.
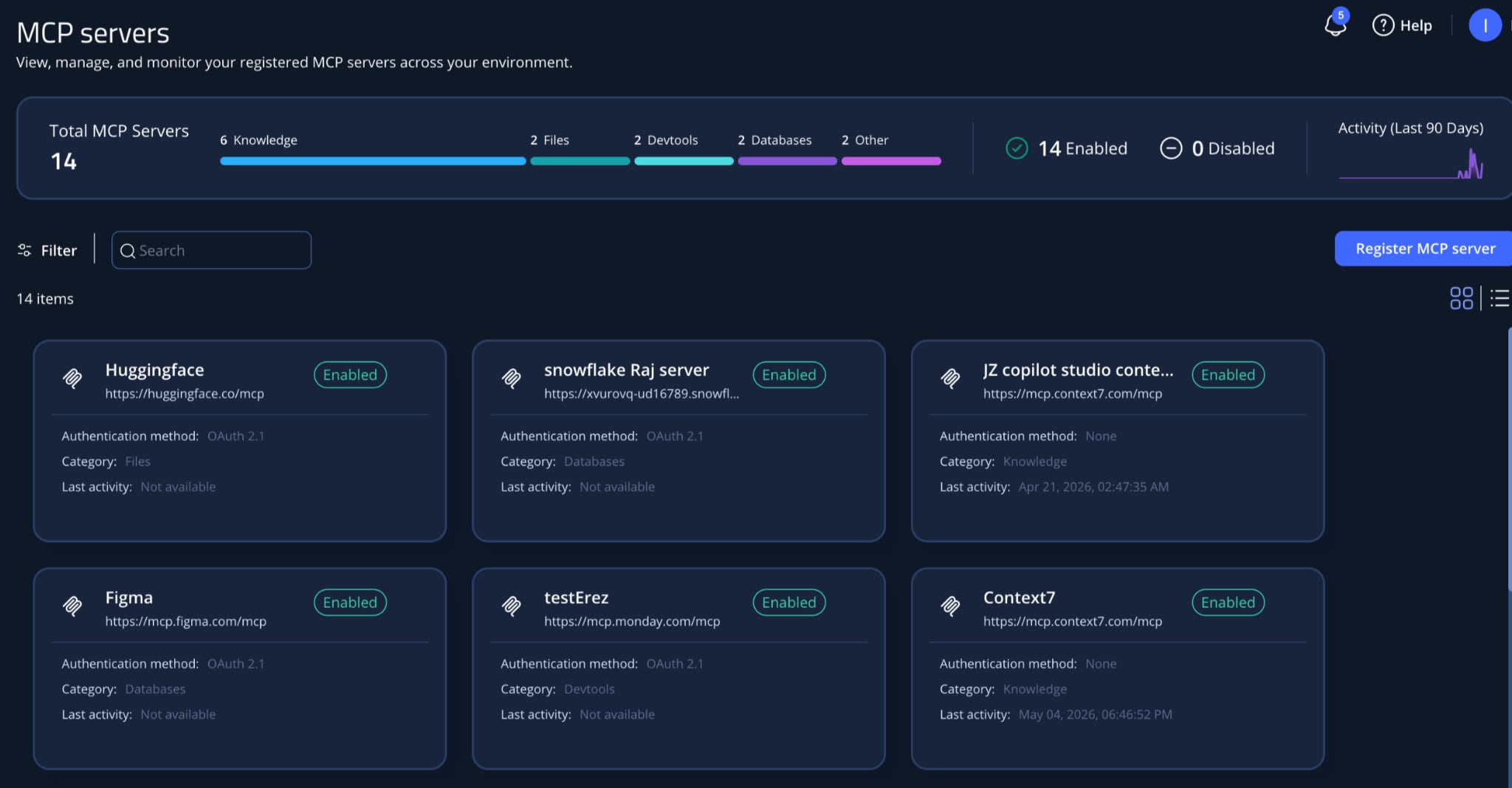
Organizations can now create an inventory of remote MCP servers, view which MCP servers are in use, see their last communication time, and identify which AI agents are pending connection or missing ownership.
This visibility also helps security teams become enablers, establishing an “approved” list of MCP servers that developers can safely give agents access to.
2. Trace AI Agents with Deep Auditing and Session Monitoring
Because all traffic is routed through the agent identity broker, security teams gain stronger traceability across agent activity. The system is designed to generate extensive audit trails for every interaction, which helps teams understand which MCP server the AI agent accessed and which tools or actions the AI agent invoked.
This helps give security teams the visibility they need to investigate and respond quickly if an agent behaves unexpectedly.
3. Control Connections with Governed MCP Access
One of the core design philosophies of Secure AI Agents is to empower developers, or builders, without compromising security.
Now, builders can (and must) proactively register new remote MCP servers to integrate with their agents. To enforce strict governance, registering an MCP server places it in a "disabled" state. A security admin must then review and explicitly mark the allowed MCP as "enabled" before AI agents can connect to it.
This approach creates a "human-in-the-loop" approval workflow that helps security teams maintain control while giving developers a clear path forward.
4. Work Wherever Agents Run with Cloud- and Agent-Agnostic Design
The solution is designed to be highly flexible for evolving AI environments. Whether security teams are relying on Google, Microsoft or custom-built solutions, Secure AI Agents supports diverse AI agents connecting to any remote MCP. This helps organizations apply consistent identity security controls as agentic AI adoption expands.
Moving Agentic AI Ahead, Securely
AI agents are a new and powerful type of identity that can act on behalf of users and operate autonomously.
Secure AI Agents helps you apply strong identity controls, such as just-in-time permissions and strict least privilege principles, transforming a potential security blind spot into a more manageable and auditable ecosystem. This is how enterprises can confidently unleash the power of AI agents without losing control over their most sensitive data.
These capabilities are now available to customers and design partners with the Secure AI Agents solution. Want to see this in practice? Join our webinar, Extend Agentic Identity Security to any MCP Server.
Prefer a tailored discussion? Speak to an expert.